Even after Anthropic released its cybersecurity model to a few users, warnings about its advanced capabilities, such as its ability to exploit software vulnerabilities, are growing, prompting enterprises to find ways to protect against the threats it poses.
In early April, the generative AI vendor released the new model under Project Glasswing, giving access to select vendors and enterprises. The model has heightened urgency among cybersecurity experts worried about its threat to software. Even Federal Reserve Chairman Jerome Powell and Treasury Secretary Scott Bessent issued warnings to banks about the increased cyber risks posed by Mythos.
The fear surrounding the model suggests that many enterprise leaders feel that, even without access to what Mythos can do, technology is now at a stage at which those who choose not to use generative AI technology risk becoming vulnerable.
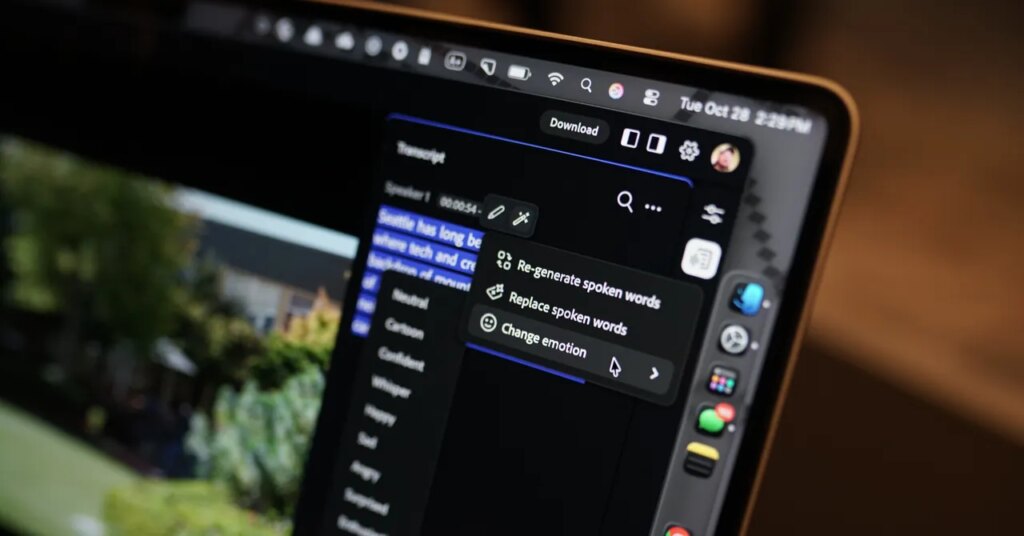
The perceived danger that the introduction of the model poses to the cybersecurity community, however, is not because Mythos is providing new capabilities that did not previously exist. It is because the model “lowers the floor for bad actors to discover vulnerabilities and create exploits,” said Rich Mogull, chief analyst at Cloud Security Alliance. The organization prepared the report “The AI Vulnerability Storm: Building a Mythos-ready Security Program.”
An Easy Target
As one of the report’s authors, Mogull said that Mythos makes it easier for malicious actors to exploit software weaknesses.
“You give it the code, type in a few commands, and it’s going to find exploitable vulnerabilities,” he said. He added that enterprises are facing “a flood that’s going to challenge our existing pacing and processes for patches.” Patches are software updates that attempt to fix vulnerabilities within an application or OS.
The fix for enterprises is to “start the work now,” Mogull added.
Therefore, although most enterprises do not have access to Mythos, Mogull said they need to act right now and prepare.
“You, as the chief information security officer, and your security team need to start using AI now,” he said. He added that while patches have long been available to cybersecurity teams, it is likely they will no longer be able to rely solely on these security updates as their only defense.
“It’s not about just being ready for Mythos and Glasswing in those patches,” Mogull said. “But about building a resilient program that can withstand the new ground rules for risk calculations.”
Getting Ready
Enterprises should realize that, even though only a few people, within a few organizations, have access to Mythos, the model’s release means it is likely to get into the wrong hands sooner rather than later, said David Nicholson, an analyst at Futurum Group.
“This is a new reality that you have to deal with,” Nicholson said. “Either get on board the train to protect yourself or just know that you’ve been notified that the world is a more vulnerable, more dangerous place, and you’re more vulnerable than ever before.”
He added that, given the likelihood that bad actors already have access to the technology, enterprises should aim to protect themselves.
“Embrace the best technology available to uncover your own vulnerabilities before bad actors do,” he said.
However, even if they embrace of stronger large language models like Mythos, enterprises should know that they still present challenges, said Gal Malachi, co-founder and CTO at Terra Security.
“[Mythos is] an amazing agent, but if it cannot authenticate, if it cannot work with guardrails, comply with the policies of the organization … it might create a lot of noise that now someone needs to go and validate and fix,” Malachi said.
That is why, even with powerful technology like Mythos, a secure software wrapper or harness is needed, he added. “As an engine, you have to have everything around that so it can give some value,” he said.
While Mythos remains a closed proprietary model, Malachi said he is sure that it will not be long before an open source version comes out from an open source-friendly vendor. An open source version of Mythos could give enterprises the ability to find ways to use the technology to defend against cyber-attacks.
“Security will stay, cybersecurity will stay. It will emerge with new techniques, hackers, and bad actors,” he said. “We always need to be one step ahead.”