IBM on Wednesday released an autonomous agentic security program, as more enterprises scramble to ensure they are ready for the impact of Anthropic’s Mythos model.
The vendor also introduced an assessment service from the vendor’s IBM Consulting unit that uses human consultants to help enterprises assess their readiness to address agentic threats by providing visibility into security gaps, policy weaknesses and AI exposures.
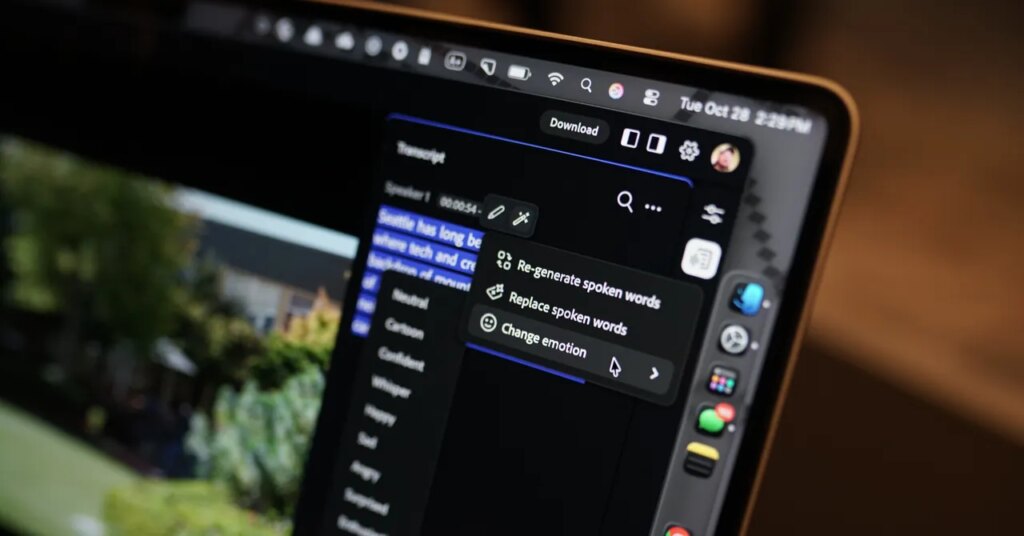
IBM Autonomous Security is a separate service that uses AI agents to analyze software exposures and runtime environments. The agents identify paths in an enterprise security environment that can be exploited, improve cyber hygiene and enforce security policies.
The IBM services come as enterprises are trying to tidy up their environments following Anthropic’s release of cybersecurity model Mythos and OpenAI’s GPT-5.4-Cyber, a specialized model to support defensive cybersecurity tasks.
While the vendors limited the release of their models, Anthropic’s model has led many enterprises to become aware of their security weaknesses, as Mythos can find thousands of zero-day vulnerabilities, software flaws that a vendor or developer is unaware of and can be exploited by hackers. Not only did Mythos identify the vulnerabilities, but it also identified ways bad actors could exploit them.
A Need to Respond to Vulnerabilities
“We now have malicious users … criminals, who can take advantage of these discoveries in machine speed time,” said Troy Leach, chief strategy officer at the Cloud Security Alliance. “Moving forward, security operations within the enterprise must adopt autonomous security capabilities to match the volume and speed of adversaries.”
He added that, as AI models reduce the level of expertise needed to produce cyberattacks, security products must “combat the speed with certain levels of autonomous responses and escalate to human security staff to confirm the actions of the agents do not drift.”
IBM Autonomous Security is an example of a product designed to prevent bad actors from exploiting AI models and normalizing strange IT behaviors, so they go undetected.
“There is optimism that AI may help [IT] architects …have a more cohesive understanding of CISOs and their security teams, with true visibility into their current security posture,” Leach said.
However, enterprises must have AI expertise to implement the systems correctly and ensure AI agents stay on the right track. There is also the challenge of cost. Enterprises must make “sure the expenditure to burn AI resources is commensurate to the security investment,” Leach said.
“The processing cost can be very expensive, similar to the early days of cloud computing and not having guardrails for automated scaling of resources only to find expensive monthly bills from the service provider,” he said.